FBI warns about Egregor Ransomware
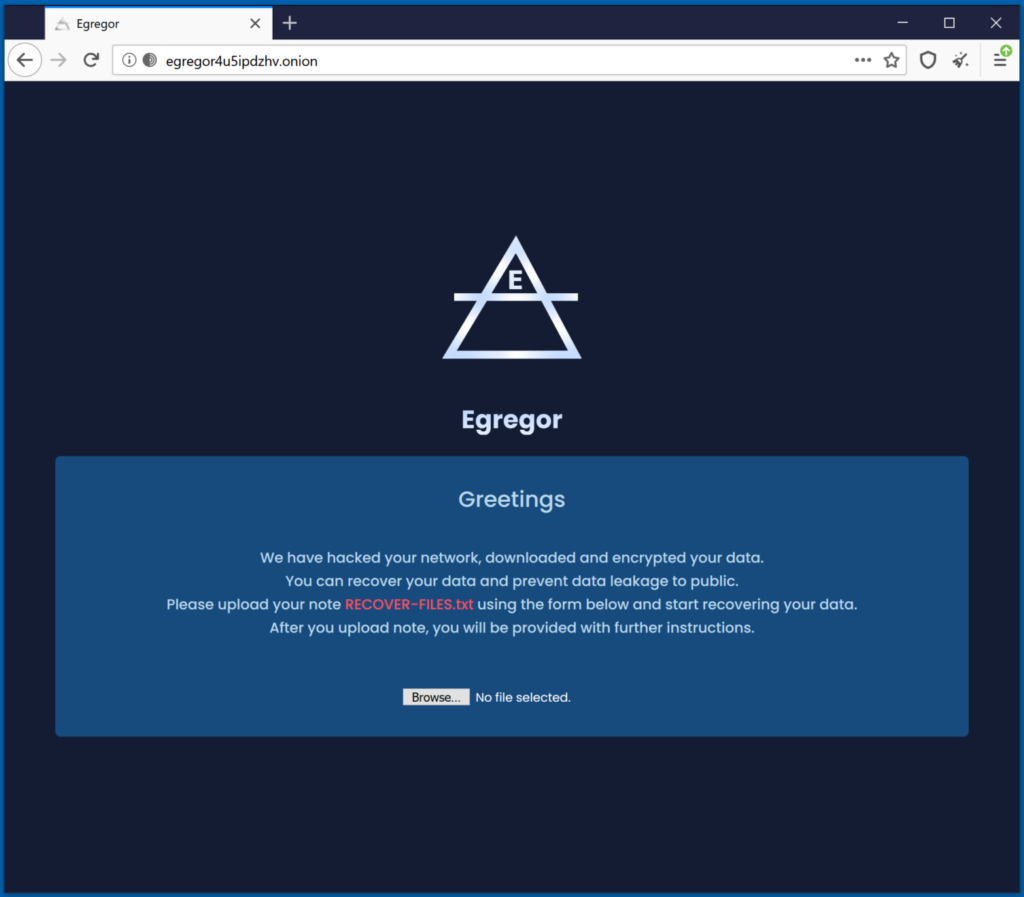
The FBI has issued an alert warning against a worldwide campaign targeting private sector companies and deploying the Egregor ransomware. The actor behind Egregor claims that 150 companies have been compromised since the beginning of the current campaign, in September 2020.
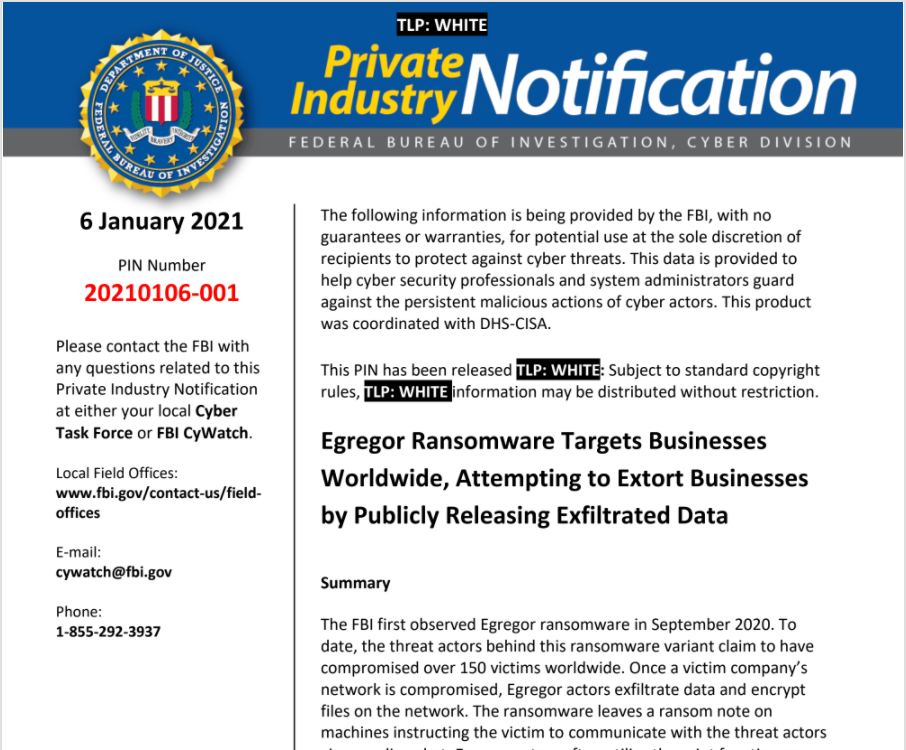
According to a post from Trendmicro, Egregor is referred as a sophisticated piece of ransomware that first surfaced around September 2020, Egregor has since been involved in a number of high-profile attacks in a short period, including attacks that were launched against major retailers and other organizations.
This ransomware is often distributed as a payload along with remote access trojans (RATs) such as QAKBOT. In turn, QAKBOT has been previously observed to be connected with the MegaCortex and ProLock ransomware families, which indicates either a possible partnership between QAKBOT and Egregor or a new payload from the QAKBOT threat actors.
What are the recent incidents involving Egregor?
A number of Egregor’s attacks have occurred against high profile targets, including a leading bookstore in October and a major retailer in December. In the former, the ransomware operators behind Egregor claimed to have gathered unencrypted financial and auditing data, although the precise nature of the data that was stolen is unclear.
Egregor has also been observed printing ransom notes. Based on analysis, printing ransom notes was not intentional on the operators’ end. Rather, it occurred as part of the ransomware’s encryption routine, which enumerates any type of network resources ؙ— including printer resources. It then connects to the network resource to encrypt files and drop the ransom note. It’s also possible that the printers and point-of-sale (POS) machines were connected to the infected machines, which resulted in the ransom notes being physically printed.
How can the impact of Egregor and other ransomware be minimized?
Although there is still no concrete evidence on how Egregor gains initial access to the system, other ransomware variants such as Maze are known to exploit vulnerabilities as part of their routine. Therefore, it is important for organizations to patch and update their systems’ software to address any exploitable vulnerabilities. Additionally, businesses are encouraged to keep their machines and their systems updated to prevent this from happening.
Businesses should also perform regular security audits of their systems to ensure that they are as secure as possible. Company data should also be periodically backed up whenever possible, preferably by adhering to the 3-2-1 rule, which involves keeping three copies in two different formats with at least one copy off-site.

Leave a Reply