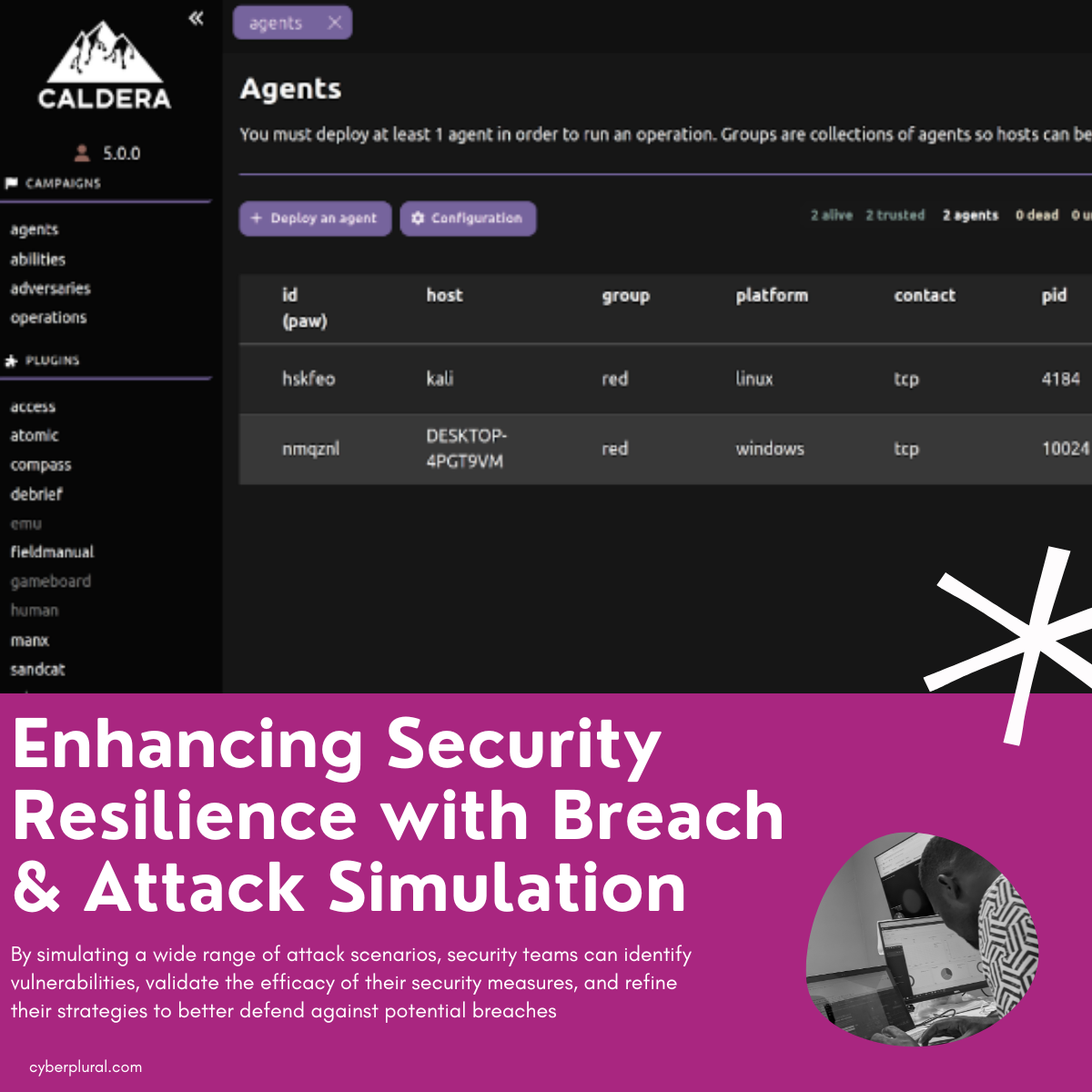
In the ever-evolving landscape of cybersecurity, organisations face an ongoing battle to stay one step ahead of threat actors. Traditional security approaches often fall short […]
Category: Security Assessment
Whitepaper: Enhancing Cybersecurity in the FinTech Ecosystem
As part of our ongoing efforts to enhance cybersecurity operations and preparedness within the fintech industry, our team tested a mock fintech application designed to […]
Active Directory Explained: Part 3 – Kerberos Authentication Protocol
Introduction In the traditional approach, users typically access computer systems by entering a password. However, this method poses a significant risk if hackers manage to […]
Active Directory Explained: Part 2 – Best Practices and Pitfalls to Avoid
Understanding IPv6 Threats in Active Directory In today’s digital world, where businesses rely on networks to operate smoothly, it’s crucial to understand how new technologies […]
Active Directory Explained: Part 1 – Best Practices and Pitfalls to Avoid
Active Directory is like a big digital phonebook for organizations that use Microsoft Windows computers. Imagine you have a big office building with lots of […]
Preventing Race Conditions in FinTech: Mitigating Security Vulnerabilities
Race conditions are a common security vulnerability that can affect financial technology (FinTech) systems. A race condition occurs when two or more processes access and […]