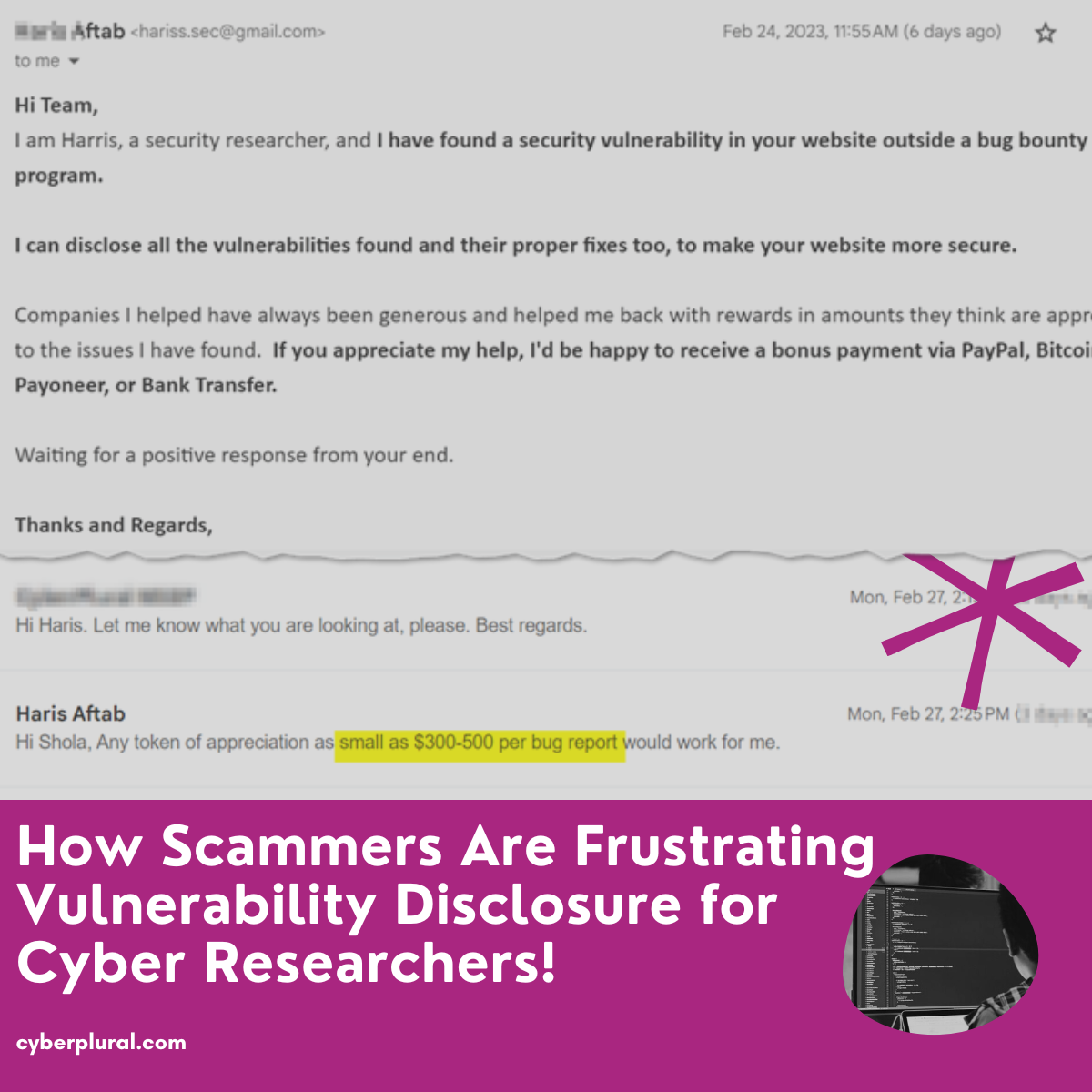
How would you react if you found this in your company inbox? You may want to ignore and many will take the fear bait and […]
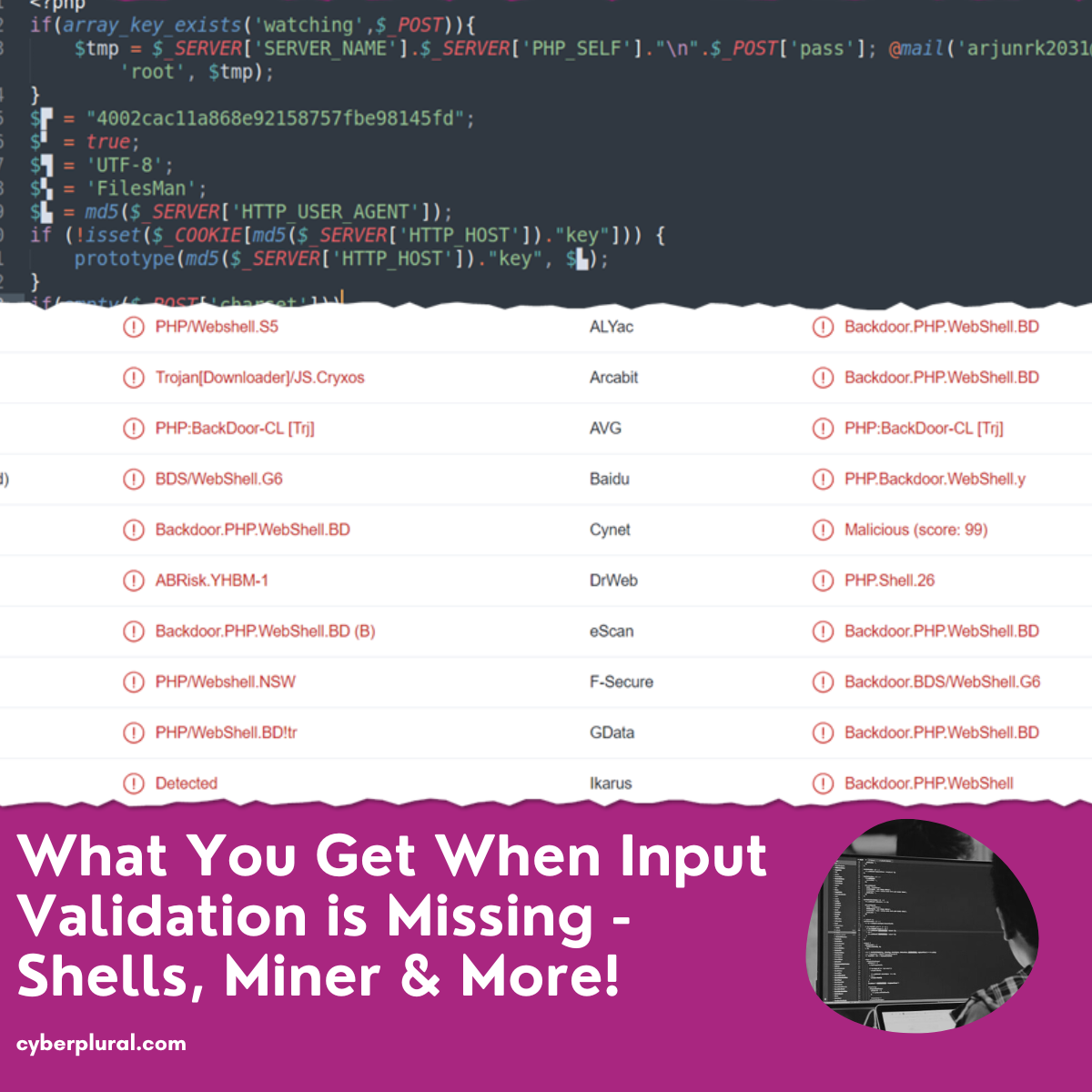
What You Get When Input Validation is Missing – Shells, Miner & More
Web applications and software frequently need user interaction to function properly. Users must be able to provide their email addresses and other personal information at […]
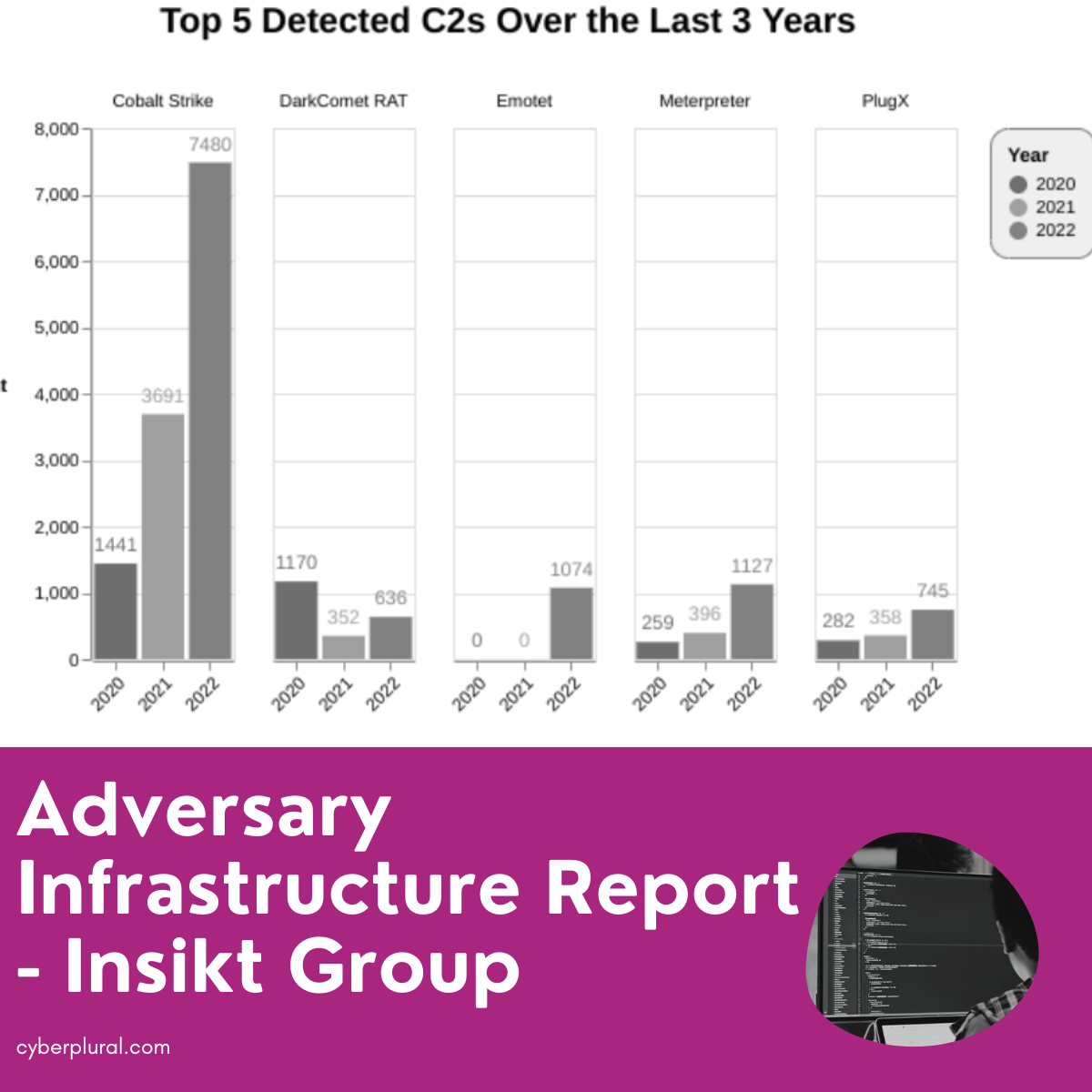
Adversary Infrastructure Report – Insikt Group
Insikt has released her 2022 Adversary Infrastructure Report. The report is based on its findings on the development of new harmful infrastructure for a variety […]
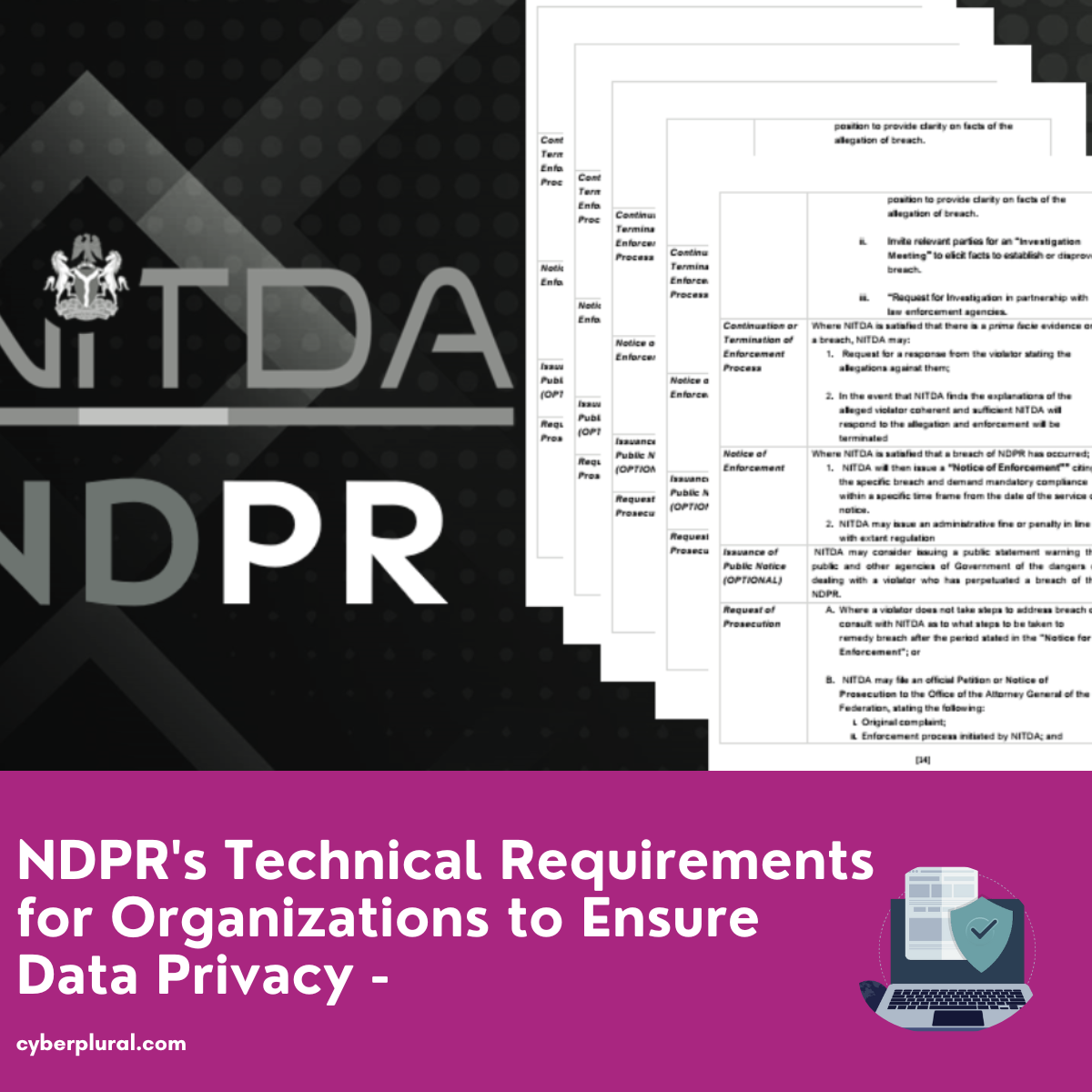
NDPR’s Technical Requirements for Organizations to Ensure Data Privacy – DPW2023
The Nigeria Data Protection Regulation (NDPR), enacted in 2019, contains a number of clauses that companies must follow in order to ensure the best possible […]
Beyond Fake INEC Portal, Threat Actor Targeting Users In 3 African Countries
Just some days ago, a fake INEC recruitment portal shows up in our space. And several media houses have reported INEC issuing a disclaimer around […]
CyberPlural Annual Report 2022
We started into the year by providing quarterly reports of what was happening with the cyber threat landscape based on what we are seeing across the globe. […]