Mitigating Windows Print Spooler “PrintNightmare” Vulnerability.

Microsoft has acknowledged the new vulnerability that affects the Windows Print Spooler service, giving attackers leverage to execute remote code with system-level privileges on all versions of Windows. This service is notable for print operation either locally or remotely in Windows which means it runs by default on client versions of the OS, Domain controllers, and several server instances of Windows.
An unpatched vulnerability could open doors for attackers from accessing endpoints and other network resources, which is why our SecOps Team has put together some handy PowerShell scripts to protect yourself until a permanent fix is released from Microsoft.
Microsoft is recommending temporary disabling of the Windows Print Spooler service or blocking of incoming connections to the print server whenever possible.
Detailed below is how you can use the script, samples were run on Windows 10. For a very big environment, system administrators can use patch management tools to push out the script as an update on all endpoints to stop the Spooler service.
Disabling Print Spooler.
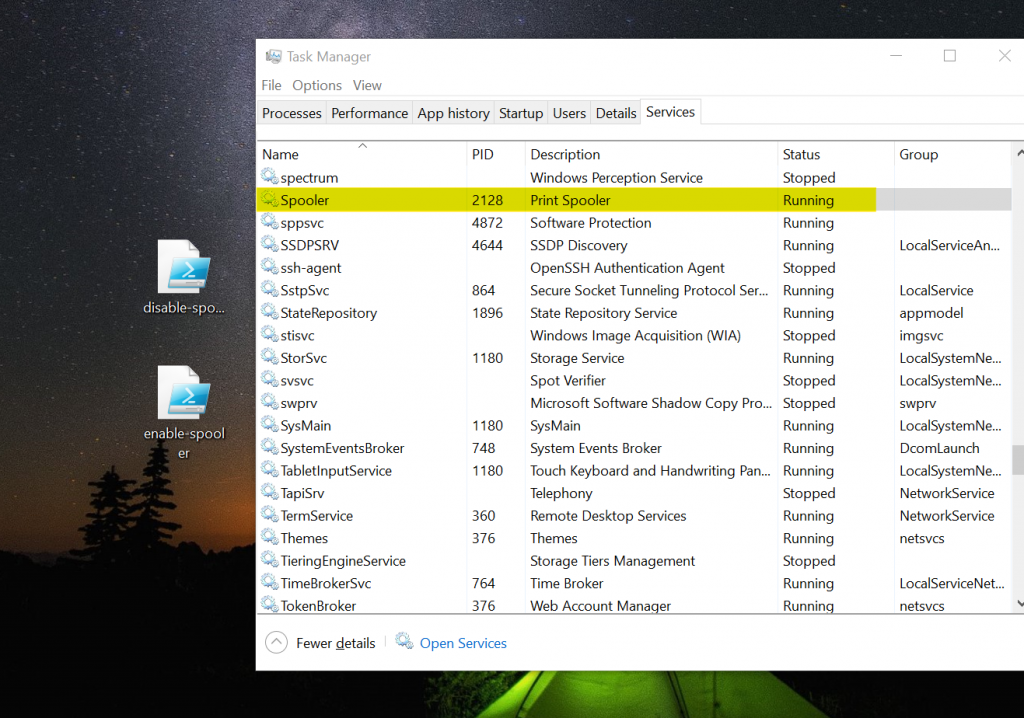
Note that once you run this script to disable the Spooler service, your devices will be protected against the PrintNightmare vulnerability, but you will no longer be able to print locally or remotely.
Also, environment that have disabled running of script on endpoints organization-wide should note that this may not work for them but script can be adapted to work with your environment.
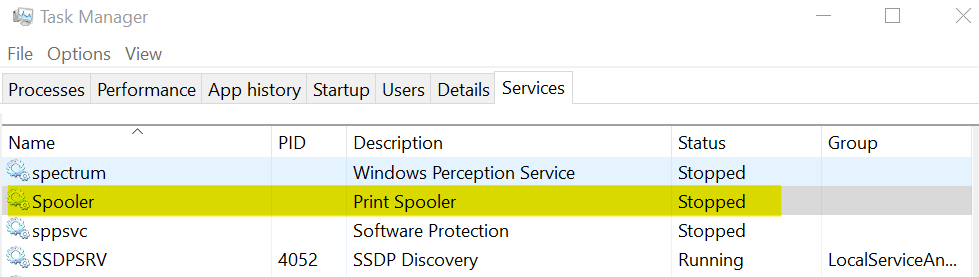
You can run enable-spooler.ps1 to restore all endpoints back to their normal state.
enable-spooler.ps1 – SHA256
227368015C02AF646FBFC0335E010E8BA4EA3790D9003A668EE43DA285106CD9
disable-spooler.ps1 – SHA256
19DEDB8D5B6B4619298477C8C3A4AB9BF7CFB787ADB33ACF8493FB66105B689C
disable-spooler.ps1
Stop-Service -Name Spooler -Force
Write-Output "Spooler service stopped"
Set-Service -Name Spooler -StartupType Disabled
Write-Output "Spooler service disabled from auto-starting on system boot"enable-spooler.ps1
Set-Service -Name Spooler -StartupType Automatic
Write-Output "Spooler service enabled to auto-start on system boot"
Start-Service -Name Spooler
Write-Output "Spooler service started"

Leave a Reply