Experts discovered a new and self-spreading Golang-based malware that targets Windows and Linux servers.
Experts from Intezer discovered a Golang-based worm that targets Windows and Linux servers.
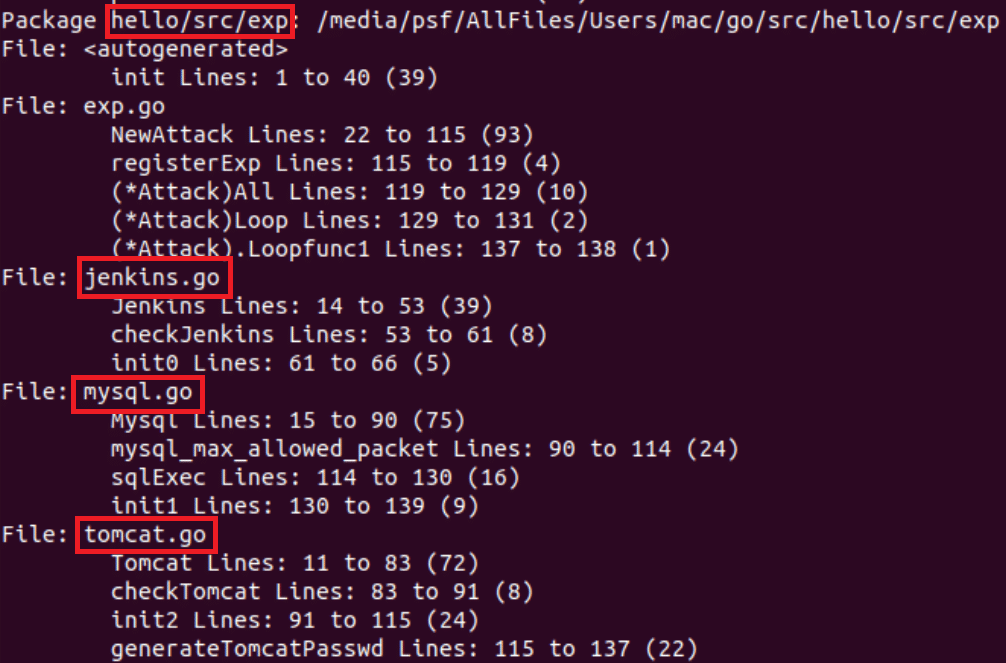
The malware has been active since early December targeting public-facing services, including MySQL, Tomcat admin panel and Jenkins that are protected with weak passwords.
The worm spreads by scanning for systems and running a credential spraying brute force attack. The malware leverages a hardcoded dictionary of weak credentials for the attack, such as root:123456.
Experts pointed out that an older version of the worm also attempted to exploit CVE-2020-14882 WebLogic’s vulnerability.
The attacks observed by the experts use three files hosted on the same C&C, a dropper script (bash or powershell), a Golang binary worm, and the XMRig Miner.
The threat actors behind this campaign have been actively updating the malicious code.
“The ELF worm binary and the bash dropper script are both fully undetected in VirusTotal at the time of this publication.” reads the analysis. “The malware behaves similarly on both Linux and Windows operating systems.”
Upon compromising a server, the malware deploys the loader script (ld.sh for Linux and ld.ps1 for Windows) that drops the XMRig miner and Golang-based worm binary.
The Linux variant of the worm checks if a process on the infected machine is listening on port 52013. The presence of the listener on this port acts as a mutex for the malicious code, it kills itself if it detects a socket for the port otherwise it will open its own socket.
Experts detailed the attack chain for both Linux and Windows servers, they also provided the following list of precautions to prevent brute force attacks and vulnerability exploits:
- Use complex passwords, limit login attempts and use 2FA (Two-Factor Authentication) if possible.
- Minimize your use of publicly facing services.
- Keep your software updated with the latest security patches.
- Use a Cloud Workload Protection Platform (CWPP), like Intezer Protect, to gain full runtime visibility over the code in your system and get alerted on any malicious or unauthorized code.
“In 2020, we saw a noticeable trend of Golang malware targeting different platforms, including Windows, Linux, Mac and Android. We assess with high confidence that this will continue in 2021.” conclude the experts.
“The fact that the worm’s code is nearly identical for both its PE and ELF malware—and the ELF malware going undetected in VirusTotal—demonstrates that Linux threats are still flying under the radar for most security and detection platforms.”

Leave a Reply