Defending against account takeover (ATO) attack.

Account takeover is a form of identity theft and fraud, where a malicious third party successfully gains access to a user’s account credentials. A successful account takeover attack leads to fraudulent transactions and unauthorized shopping from the victim’s compromised financial accounts.
Understanding the cyber kill chain of an ATO attack which is on the rise can position defenders and fraud teams to successfully stop threat actors in the early phases of the attack by deploying and using appropriate defenses to help bring down the risk to organizations and end-user who are directly impacted.
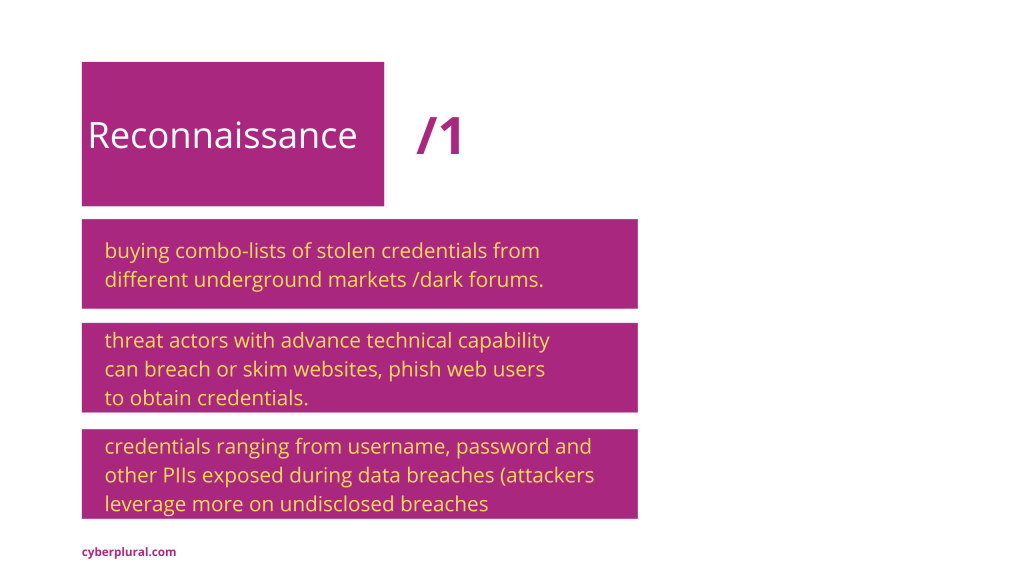
Just like any other attack, reconnaissance is the first phase of the account takeover (ATO) attacks where threat actors relied on underlying support structures like the dark / deep web to gather credentials – mostly by buying combo-lists of stolen credentials from different underground markets, chatroom and sites. Threat actors with advance technical capability can breach or skim websites, phish web users to obtain credentials for direct usage or to further monetize them by putting them up for sale on underground markets. Credentials ranging from the username, password and other PIIs exposed during data breaches (attackers leverage more on undisclosed breaches, where post-incident remediation have not been applied to stolen credentials as this ensure less false positive rate in the second stage and next) are often time caught up in the process of this initial recon.
How can the gathered credential from above be weaponized?
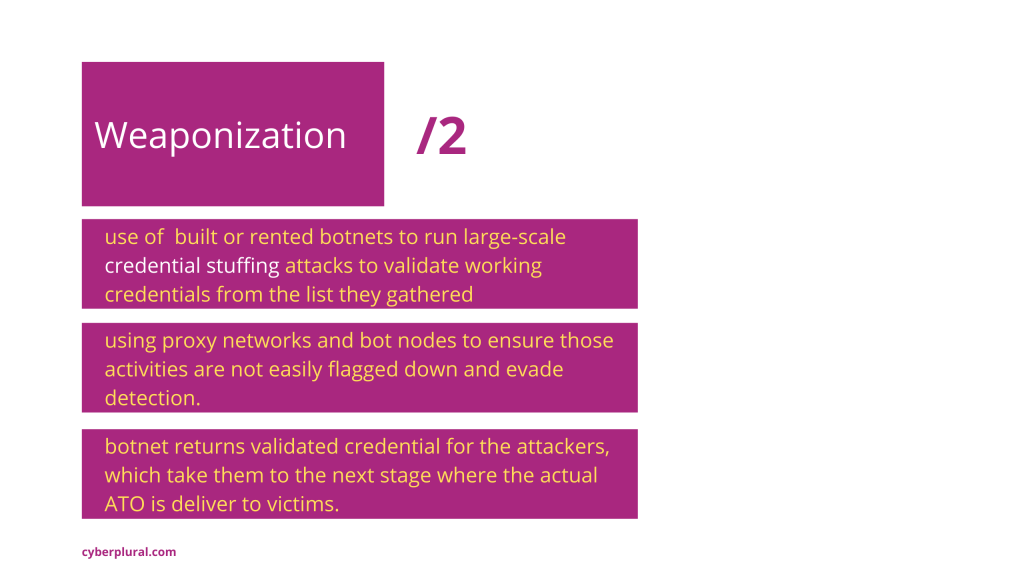
At this stage, attackers take advantage of built or rented botnets to run large-scale credential stuffing attacks to validate working credentials from the list they gathered. Targeted websites could be financial and e-commerce /shopping platforms. Some level of obfuscation techniques is done here to increase the level of success, attackers have resulted in using proxy networks and bot nodes to ensure those activities are not easily flagged down and evade detection.
Using some tools also required the attackers to make sure their activity resemble what is coming from real users to the targeted platform. Manipulating activity to look like they are coming from the home network and ISP-based addresses as botnets connectivity are proxied through compromised devices located on the home network to further evade detection. Threat actors understand that rulesets that can flag down out-of-country IP addresses, datacenter IP address from cloud service provider already existed that are reducing their chances of success and the need to re-strategize arise to stay on top of their game.
The botnet returns validated credentials for the attackers, which take them to the next stage where the actual ATO delivers to the victim – as they only require a small percentage of the tested list to have their hands on the final objective. Validated accounts can be put up for sale on the dark web/telegram channels or be put into use by the same group that validated them for account takeover (ATO).
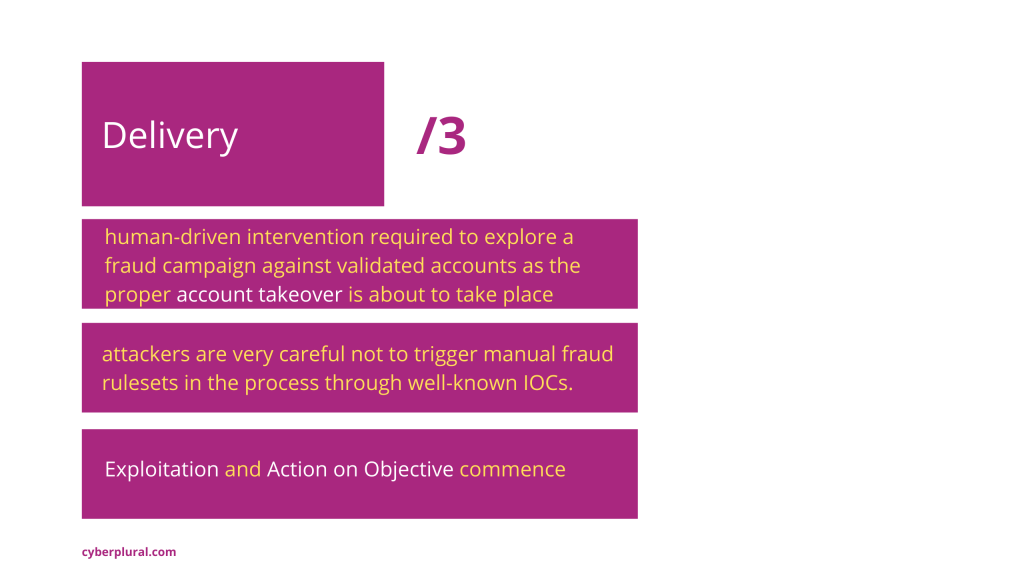
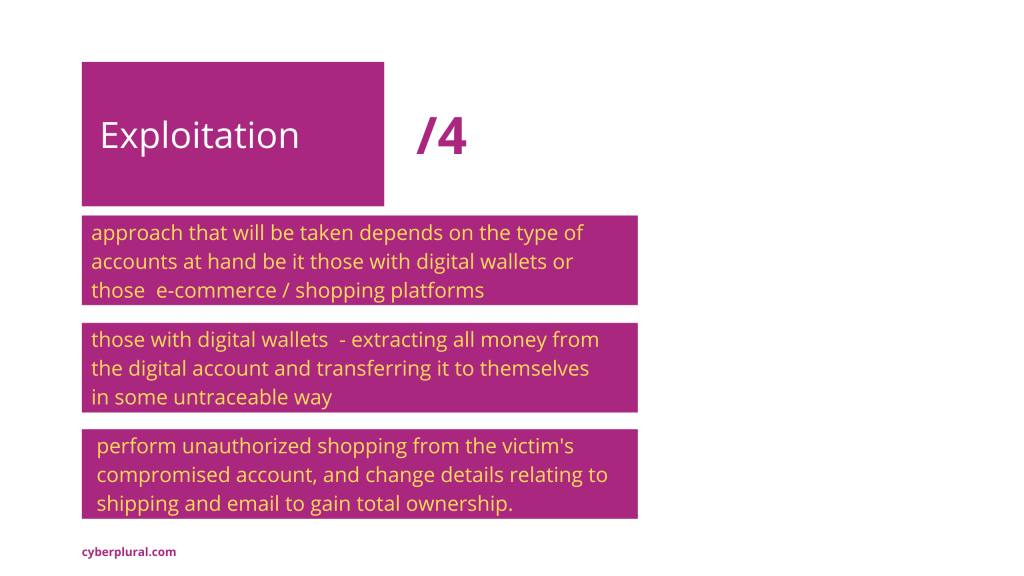
This stage involves series of human-driven interventions that will explore a fraud campaign against validated accounts as the proper account takeover is about to take place. The approach that will be taken depends on the type of account they have at hand, for accounts that have digital wallets, they will be performing the process of money-muling, which involves extracting that money from the digital account and transferring it to themselves in some untraceable way.
For accounts that are related to eCommerce / shopping platforms, they will perform unauthorized shopping from the victim’s compromised account, and change a couple of details around shipping and email to gain total ownership of the account. Attackers are very careful not to trigger manual fraud rulesets in the process through well-known IOCs, such as notice of recent changes to email addresses, presented with secondary authentication requests from the platform.
Deploying asymmetric detection capabilities is known to have been very good at stopping/slowing down the ATO threat actors at this stage where human interaction is needed to make them achieve their final objective. Account protection technology like this lookout for risk profiles relating to location, devices types, and header information in real-time to determine whether to authenticate such requested login attempt, without alerting the would-be ATO attackers – all of these features are more of a dynamic profile that is now been easily mimicked by attackers.
Which means switching to monitoring Indicator of Behaviour (IoB) from real human can help to increase the fidelity of stopping manual fraudsters. This involves building a database of what valid accounts owners look like when they connect. Profiling that will be done over time uniquely matching these activities to every login request before future access is granted. Information such as what device account owners last came from when they successfully logged in, or what ISP frequent the list of this access, and metadata that can bring in more uniqueness. It delivers more insight into determining who (the real valid account owner or ATO attacker) is making a request to login, these are traits that are more difficult to emulate for threat actors.
This can further escalate the system to generate a step-up authentication, one-time password (OTP) challenge to ensure users can validate themselves to be known good users and not ATO attackers. All activity/incident logs from the system can be passed onto the defenders/fraud team to further understand the associated risk score for detecting ATO attackers before they compromise customer account.
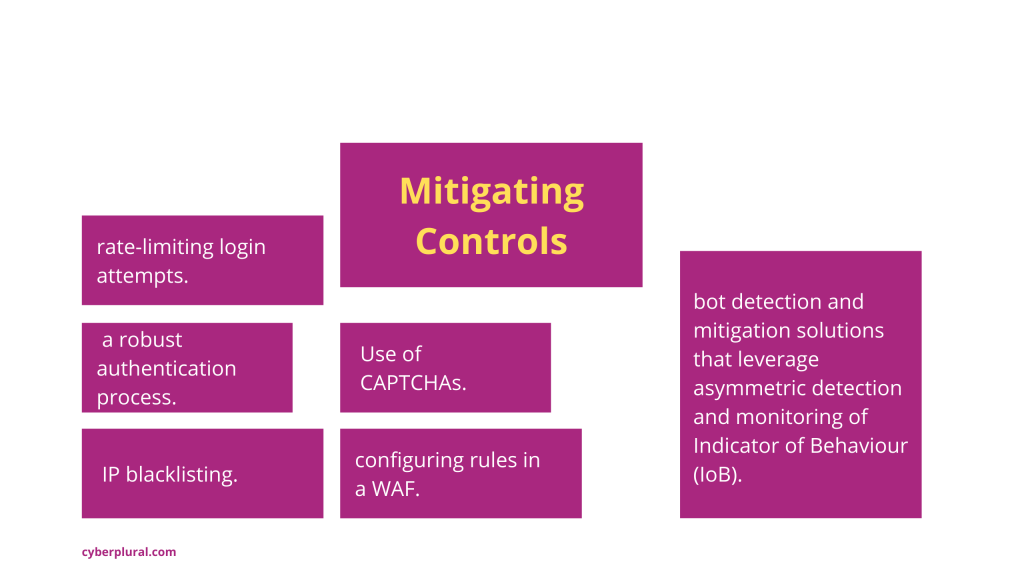
Many controls are used by online businesses to eliminate and prevent account takeover attempts. The list includes practices such as limiting login attempts, a robust authentication process, IP blacklisting, configuring rules in a WAF, CAPTCHAs and bot detection and mitigation solutions that leverage asymmetric detection and monitoring of Indicator of Behaviour (IoB) from real humans have emerged as off-the-shelf controls to eliminate account takeover attempts.

Leave a Reply