Agent Tesla (RAT) Operators Arrested In Nigeria
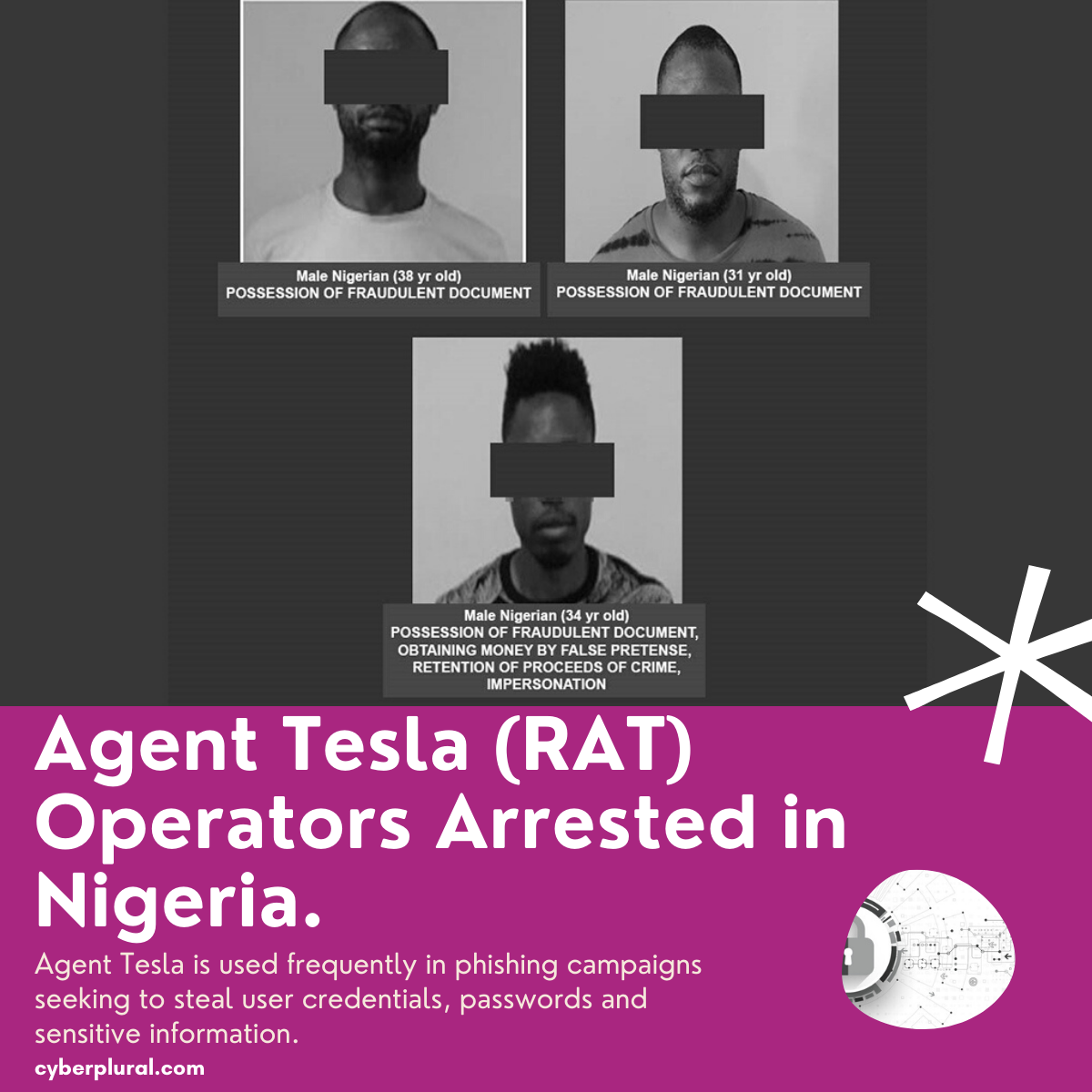
Just a few days back, three Nigerians were arrested in the INTERPOL operation codename Killer Bee. The arrests follow the publication of an INTERPOL Cyber Report linking a suspected syndicate of Nigerian fraudsters operating from West Africa to the use of a malicious Remote Access Trojan (RAT) known as Agent Tesla.
A bit about Agent Tesla
Agent Tesla which has been active for over seven years has been used frequently in phishing campaigns seeking to steal user credentials, passwords and sensitive information.
First observed in the wild in 2014, Agent Tesla has gone through many iterations and development introducing new capabilities for causing mayhem and escaping detection along the way. It has used these features to maintain itself as one of the most prevalent Remote Access Trojans (RAT) across the cyber threat landscape.
This popular information-stealing Trojan is being sold and distributed (malware-as-a-service) across a number of underground hacking forums and platforms with its highly customizable features, which allow threat actors to tailor it to their particular needs.
Back to the arrest
The suspects are thought to have used RAT to reroute financial transactions stealing online connection details from corporate organizations, including oil and gas companies in Southeast Asia, the Middle East, and North Africa.
The three suspects aged between 31 and 38, were each arrested in possession of fake documents, including fraudulent invoices and forged official letters. Examination of devices such as laptops and mobile phones seized during the EFCC-led arrest in Lagos and Benin also validate the systematic use of the Agent Tesla malware to divert monetary transactions from victims to their own accounts.
The EFCC’s Director of Operations, Abdulkarim Chukkol believed this enforcement led action will send a clear message to perpetrators, that cybercrime will have serious repercussions, especially for those involved in business email compromise (BEC) and fraud, particularly in Nigeria.
How to Protect Yourself from Agent Tesla.
Since the emergence of the malware and its prevalent usage especially during the pandemic, several threat researchers and security companies have worked to ensure that activities of the malware can be detected and businesses can be protected against it regardless of its continuous evolvement.
The well-known delivery method for Agent Tesla is malicious spam (which is what we are all familiar with). Most time the email accounts used to spread Agent Tesla are often legitimate accounts that have been compromised. Businesses, Organizations and individuals should, as always, treat email attachments from unknown senders with caution, and verify attachments before opening them.
Enterprise should have in place controls that can help automate the disruption of these cyber kill chain stages most especially delivery, installation and execution. With CyberPlural, businesses can leverage our services for the implementation and management of such controls while they focus on their core objectives.

Leave a Reply